Microsoft Hacked in Russia-Linked SolarWinds Cyberattack -- Update
December 31 2020 - 3:25PM
Dow Jones News
By Robert McMillan
The Russia-linked hackers behind a widespread cyber-intrusion
into U.S. corporate and government systems were able to access
internal systems within Microsoft Corp. and view internal source
code, used to build software products, the company said
Thursday.
Microsoft had previously confirmed that it had downloaded
malicious software from a vendor called SolarWinds Corp. that had
been modified by the hackers. Thursday's disclosure is the first
indication that the hackers were able to access internal systems at
Microsoft.
"We detected unusual activity with a small number of internal
accounts and upon review, we discovered one account had been used
to view source code in a number of source code repositories,"
Microsoft said in a statement.
This compromised account was able to view Microsoft's source
code, but not make changes, the company said.
Microsoft's disclosure raises the specter that the hackers may
have targeted and then compromised other technology companies as
well, said Sherri Davidoff, chief executive of the security
consulting firm LMG Security LLC. "That's why these hackers are
going after these companies, " she said. "They don't want access to
just one company. They want access to everything."
A Microsoft spokesman declined to say what products or internal
systems were affected by the intrusion.
The company has "found no evidence of access to production
services or customer data," and "no indications that our systems
were used to attack others," the company said.
The SolarWinds attack dates back to at least October of 2019 and
has prompted a flurry of cyber investigations within government and
private industry. Through a backdoor the attackers installed in
SolarWinds's Orion networking software, the hackers found their way
into systems belonging to the Department of Homeland Security, the
State Department, the Treasury and Commerce departments and
others.
U.S. government and cybersecurity officials have linked the
attack to Russia. The Kremlin has denied involvement in the
hacks.
A Wall Street Journal analysis of internet records identified
infected computers at two dozen organizations that installed the
tainted network monitoring software from SolarWinds. Among them:
technology giant Cisco Systems Inc., chip makers Intel Corp. and
Nvidia Corp., and accounting firm Deloitte LLP.
The hackers also compromised at least one reseller of
Microsoft's cloud-based computing services and tried to use that as
a way of gaining access to emails belonging to the cybersecurity
vendor CrowdStrike Inc. That attempt was unsuccessful, CrowdStrike
said last week. Microsoft is the world's second-largest
cloud-computing company after Amazon.com Inc.
The SolarWinds attack went undetected for months and was
discovered by FireEye Inc., a cybersecurity company, when hackers
tripped an alarm. FireEye put more than 100 cyber sleuths on the
job of investigating the hack of its systems, before ultimately
zeroing in on SolarWinds' software as the source of the
compromise.
U.S. government and corporate Investigators are still trying to
assess what information the hackers were able to glean in what
cybersecurity officials have characterized as one of the biggest
breaches of U.S. networks in years.
Software development technologies have long been considered a
sensitive target in cyberattacks. Source code management systems,
like the one accessed by the Microsoft hackers, are used by
software developers to build their products. Gaining access to them
could give hackers insight into new ways of attacking these
products, security experts say.
"Having the source code might reduce the amount of time and
analysis for identifying vulnerabilities but attackers are still
able to identify vulnerabilities without source code," said Window
Snyder, formerly chief security officer at Square Inc. "It's
another tool in the toolbox."
In the case of SolarWinds, the attackers were able to do more
than simply view source code. They compromised the system
SolarWinds used for assembling its finished software products and
were able to slip malicious code into SolarWinds' own software
updates that were shipped to about 18,000 customers, including
Microsoft and FireEye.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
December 31, 2020 16:10 ET (21:10 GMT)
Copyright (c) 2020 Dow Jones & Company, Inc.
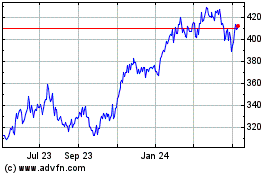
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Mar 2024 to Apr 2024
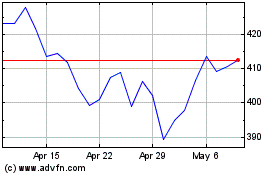
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Apr 2023 to Apr 2024