SolarWinds Hackers' Attack on Email Security Company Raises New Red Flags
January 12 2021 - 10:29PM
Dow Jones News
By Robert McMillan
A breach at email security provider Mimecast Inc. underscores
that Russia-linked hackers appear to have targeted victims along
multiple avenues of attack in what is shaping up to be one of the
most successful cyber campaigns of U.S. government and corporate
systems.
The attack potentially adds thousands of victims to the
yearslong intelligence operation and likely aimed at gaining access
to email systems, security experts say. Mimecast, in a Tuesday blog
post, said the hackers were able to obtain a digital certificate
used by the company to access its customers' Microsoft 365 office
productivity services.
The Mimecast hackers used tools and techniques that link them to
the hackers who broke into Austin, Texas-based SolarWinds Corp.,
according to people familiar with the investigation. The link to
the SolarWinds hackers was reported earlier by Reuters.
U.S. government officials have blamed Russia for the SolarWinds
attack. Moscow has denied involvement.
Most of the companies and government agencies identified as
victims to date were compromised via a piece of network management
software called Orion that belongs to SolarWinds. But the Mimecast
case, in which the vendor's customers became targets, highlights
that not all victims had to be SolarWinds users themselves to be
targeted.
Lexington, Mass.-based Mimecast said the hack potentially
affected 10% of its users, or about 4,000 customers. The company
added that likely only a low single-digit number of victims were
targeted. Mimecast markets its services as helping customers
protect themselves from ransomware attacks attempted via email
attachments and providing other protections for sensitive business
information.
The hackers may have gained access to Mimecast itself without
the SolarWinds software. The email service provider once was a
SolarWinds customer, but no longer uses its Orion network
management software, according to a person familiar with the
matter. The company hasn't determined how it was breached and if
its earlier use of SolarWinds software enabled the hackers.
It is the latest twist in a wide-ranging hack whose breadth and
sophistication has alarmed security experts and government
agencies.
"This is a massive concerted attack against a number of
targets," said Glenn Chisholm, chief executive with Obsidian
Security Inc., a security company that is investigating some of the
intrusions.
Last week, the Department of Homeland Security warned that the
SolarWinds hackers were using a variety of techniques aside from
the compromised Orion software to break into their victims'
companies, including guessing passwords and taking advantage of
administrative credentials to systems that hadn't been properly
secured.
The hackers also compromised at least one reseller of
Microsoft's cloud-based computing services and tried to use that as
a way of gaining access to emails belonging to the cybersecurity
vendor CrowdStrike Inc. That attempt was unsuccessful, CrowdStrike
has said.
With Mimecast digital certificates in hand, the hackers would
likely be able to read email or other sensitive information stored
on the Microsoft Exchange servers, Mr. Chisholm said.
In the SolarWinds break-in, the hackers created a malicious
software update that was then shipped to customers and used to
break into potentially hundreds of other companies.
SolarWinds says that about 18,000 of its customers ended up
downloading malicious software, which was snuck into unsuspecting
networks as an update to Orion.
SolarWinds this week said it found evidence the attack on its
systems began at least a month earlier than first disclosed.
Mimecast learned of the hack from Microsoft, which has been
investigating the SolarWinds breach, and which earlier disclosed
that its internal software source code had been accessed by these
hackers. Another security company, FireEye Inc was also compromised
by the hackers.
A Microsoft Corp. spokeswoman said that the Mimecast certificate
was obtained by a "sophisticated actor." Microsoft 365 users who
don't use Mimecast are unaffected by the incident, she said.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
January 12, 2021 23:14 ET (04:14 GMT)
Copyright (c) 2021 Dow Jones & Company, Inc.
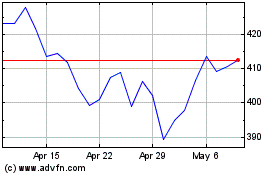
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Apr 2024 to May 2024
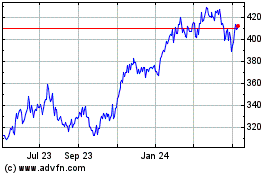
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From May 2023 to May 2024