Fortinet Threat Landscape Report Reveals
Over One-quarter of Organizations Experienced a Mobile Malware
Attack
Phil Quade, Chief Information Security Officer,
Fortinet“Cyberthreats are growing rapidly and every
organization is feeling the impact, with daily detections and
exploits increasing. Previously, ransomware was the talk of the
day, and now cryptojacking, mobile malware, and attacks against
business-critical supply chains are proliferating. As our cyber
adversaries continue to incorporate new threats and leverage
increasingly automated techniques at speed and scale for their
malicious activities, segmentation and integration have become
critical security strategies for IT and OT environments today.”
News Summary:Fortinet® (NASDAQ: FTNT), a global
leader in broad, integrated, and automated cybersecurity solutions,
today announced the findings of its latest quarterly Global
Threat Landscape Report. The research reveals threats are
increasing and evolving to become more sophisticated. Unique threat
variants and families are on the rise, while botnet infections
continue to infect organizations. For a detailed view of the Threat
Landscape Indices for exploits, botnets, and malware as well as
some important takeaways for CISOs read the blog. Highlights of the
report follow:
- Threat Development Continues to Be a Top Focus for
Cybercriminals. Cybercriminals are not only expanding
their attack arsenal but also developing new strategies for
breaching defenses. Unique malware variants grew 43%, while the
number of malware families grew by nearly 32%. The number of unique
daily malware detections per firm also rose 62%. In line with these
trends, unique exploits increased nearly 10% and the number of
exploit detections per firm rose 37%. Cybercriminals continue to
evolve threats by creating unique malware variants and families,
demonstrating the ongoing importance of threat intelligence and
assessment tools.
- Mobile Devices Remain a Target. Over
one-quarter of organizations experienced a mobile malware attack,
with the majority being on the Android operating system. In fact,
of the threats organizations faced from all attack vectors, 14% of
total malware alerts were Android related. By comparison, only
.000311% of threats were targeted at Apple iOS. Mobile threats are
a looming threat that must be addressed, especially as the
mobile-shopping holiday season nears. These threats can become a
gateway for corporate networks to be exploited. Criminals know
mobile is an accessible target for infiltrating a network, and they
are exploiting it.
- Cryptojacking is a Gateway to Other Attacks.
Cryptojacking remains prevalent and continues to grow in scope. The
number of platforms affected by cryptojacking jumped 38% and the
number of unique signatures nearly doubled in the past year. These
include new sophisticated platforms for advanced attackers as well
as “as-a-service” platforms for novice criminals. IoT botnets are
also increasingly leveraging cryptojacking exploits for their
attack strategy. Although it is often considered to be a nuisance
threat that simply hijacks unused CPU cycles, security leaders are
realizing how cryptojacking can become a gateway for additional
attacks. Underestimating the repercussions of cryptojacking places
an organization under heightened risk.
- Percentage of Malicious Network Traffic is Higher on
Weekends or Holidays. Data shows malicious network traffic
represents a higher percentage of overall traffic on weekends and
holidays as business traffic slows down significantly since many
employees are not working during this time. For many organizations
this may be an opportune time to sweep for malware because as the
“haystack” of traffic becomes smaller, the chance of finding
malicious “needles” is much greater. With cybercriminals using more
automated and sophisticated techniques, any opportunity to increase
visibility can be an advantage.
- Burstiness of Botnets. The botnet index rose
only 2%, though the number of infection days per firm increased 34%
from 7.6 days to 10.2 days. This may be an indication that botnets
are becoming more sophisticated, difficult to detect, or harder to
remove. It may also denote a failure to practice good cyber hygiene
in general by some organizations. The importance of consistent
security hygiene remains vital to thoroughly addressing the total
scope of these attacks. Sometimes botnets can go dormant, only to
return after normal business operations have resumed, if the root
cause or “patient zero” is not determined.
- Encrypted Traffic Reaches a New Threshold.
Encrypted traffic reached a new high, comprising 72% of all network
traffic, up from 55% just one year ago. While encryption can
certainly help protect data in motion as it moves between core,
cloud, and endpoint environments, it also represents a challenge
for traditional security solutions. The critical firewall and IPS
performance limitations of some legacy security solutions continue
to limit the ability of organizations to inspect encrypted data at
business speeds. As a result, a growing percentage of this traffic
is increasingly not analyzed for malicious activity, making it an
ideal mechanism for criminals to spread malware or exfiltrate
data.
Digital Change Requires a New Approach to
Security
The threat data in this quarter’s report once again reinforces
many of the threat prediction trends unveiled by the FortiGuard
Labs global research team. To stay ahead of the ongoing efforts of
cybercriminals, organizations need to transform their security
strategies as part of their digital transformation efforts.
Isolated, legacy security devices and poor security hygiene
continue to be a formula for increased risk to today’s threat
landscape as they do not provide adequate visibility or control.
Instead, a security fabric that spans the entire expanded network
environment and is integrated between each security element is
vital to address today’s growing threat environment and to protect
the expanding attack surface. This approach enables actionable
threat intelligence to be shared at speed and scale, shrinks the
necessary windows of detection, and provides the automated
remediation required for today’s multi-vector exploits.
Report and Index Overview The Fortinet Threat
Landscape Report is a quarterly view that represents the collective
intelligence of FortiGuard Labs drawn from Fortinet’s vast array of
global sensors during Q3 2018. Research data covers global and
regional perspectives. Also included in the report is the Fortinet
Threat Landscape Index (TLI), comprised of individual indices for
three central and complementary aspects of that landscape which are
exploits, malware, and botnets, showing prevalence and volume in a
given quarter. The report also examines important zero-day
vulnerabilities and infrastructure trends to add context about the
trajectory of cyberattacks affecting organizations over time.
Additional Resources
- Read our blog for more information about the research or to
access the full threat report.
- View the Fortinet Threat Landscape Indices for botnets,
malware, and exploits for Q3, 2018.
- Learn more about FortiGuard Labs and the FortiGuard Security
Services portfolio.
- Learn more about the FortiGuard Security Rating Service, which
provides security audits and best practices.
- Sign up for the weekly FortiGuard Threat Intelligence
Briefs.
- Read more about our Network Security Expert program, Network
Security Academy program or our FortiVets program.
- Read more about the Fortinet Security Fabric or the Third
Generation of Network Security.
- Follow Fortinet on Twitter, LinkedIn, Facebook,
YouTube, and Instagram.
About FortinetFortinet (NASDAQ: FTNT) secures
the largest enterprise, service provider, and government
organizations around the world. Fortinet empowers its customers
with intelligent, seamless protection across the expanding attack
surface and the power to take on ever-increasing performance
requirements of the borderless network - today and into the future.
Only the Fortinet Security Fabric architecture can deliver security
without compromise to address the most critical security
challenges, whether in networked, application, cloud, or mobile
environments. Fortinet ranks #1 in the most security appliances
shipped worldwide and more than 375,000 customers trust Fortinet to
protect their businesses. Learn more
at http://www.fortinet.com, the Fortinet Blog, or FortiGuard
Labs.
FTNT-O
Copyright © 2018 Fortinet, Inc. All rights reserved. The symbols
® and ™ denote respectively federally registered trademarks and
common law trademarks of Fortinet, Inc., its subsidiaries and
affiliates. Fortinet's trademarks include, but are not limited to,
the following: Fortinet, FortiGate, FortiGuard, FortiCare,
FortiManager, FortiAnalyzer, FortiOS, FortiADC, FortiAP,
FortiAppMonitor, FortiASIC, FortiAuthenticator, FortiBridge,
FortiCache, FortiCamera, FortiCASB, FortiClient, FortiCloud,
FortiConnect, FortiController, FortiConverter, FortiDB, FortiDDoS,
FortiExplorer, FortiExtender, FortiFone, FortiCarrier,
FortiHypervisor, FortiIsolator, FortiMail, FortiMonitor, FortiNAC,
FortiPlanner, FortiPortal, FortiPresence , FortiProxy,
FortiRecorder, FortiSandbox, FortiSIEM, FortiSwitch, FortiTester,
FortiToken, FortiVoice, FortiWAN, FortiWeb, FortiWiFi, FortiWLC,
FortiWLCOS and FortiWLM.
Other trademarks belong to their respective owners. Fortinet has
not independently verified statements or certifications herein
attributed to third parties and Fortinet does not independently
endorse such statements. Notwithstanding anything to the contrary
herein, nothing herein constitutes a warranty, guarantee, contract,
binding specification or other binding commitment by Fortinet or
any indication of intent related to a binding commitment, and
performance and other specification information herein may be
unique to certain environments. This news release may contain
forward-looking statements that involve uncertainties and
assumptions, such as statements regarding technology releases among
others. Changes of circumstances, product release delays, or other
risks as stated in our filings with the Securities and Exchange
Commission, located at www.sec.gov, may cause results to
differ materially from those expressed or implied in this press
release. If the uncertainties materialize or the assumptions prove
incorrect, results may differ materially from those expressed or
implied by such forward-looking statements and assumptions. All
statements other than statements of historical fact are statements
that could be deemed forward-looking statements. Fortinet assumes
no obligation to update any forward-looking statements, and
expressly disclaims any obligation to update these forward-looking
statements.
| |
|
|
| Media
Contact: |
Investor
Contact: |
Analyst
Contact: |
| |
|
|
| John Welton |
Peter Salkowski |
Ron Davis |
| Fortinet, Inc. |
Fortinet, Inc. |
Fortinet, Inc. |
| 408-235-7700 |
408-331-4595 |
415-806-9892 |
| pr@fortinet.com |
psalkowski@fortinet.com |
rdavis@fortinet.com |
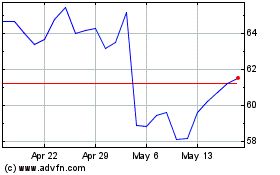
Fortinet (NASDAQ:FTNT)
Historical Stock Chart
From Apr 2024 to May 2024
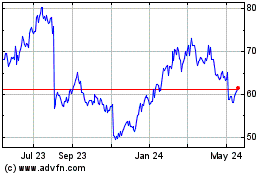
Fortinet (NASDAQ:FTNT)
Historical Stock Chart
From May 2023 to May 2024