Corero Warns of Powerful New DDoS Attack Vector with Potential for Terabit-Scale DDoS Events
October 25 2016 - 7:00AM
Business Wire
New zero-day attack vector has significant
amplification factor and could be used to enhance effectiveness of
botnet tools used to launch recent attacks on Dyn, Krebs on
Security and OVH
Corero Network Security (LSE: CNS), a leading provider of First
Line of Defense® security solutions against DDoS attacks, has today
disclosed a significant new zero-day DDoS attack vector observed
for the first time against its customers last week. The new
technique is an amplification attack, which utilizes the
Lightweight Directory Access Protocol (LDAP): one of the most
widely used protocols for accessing username and password
information in databases like Active Directory, which is integrated
in most online servers.
While Corero’s team of DDoS mitigation experts has so far only
observed a handful of short but extremely powerful attacks against
their protected customers originating from this vector; the
technique has potential to inflict significant damage by leveraging
an amplification factor seen at a peak of as much as 55x.
Therefore, in terms of its potential scale, if combined with the
Internet of Things botnet that was utilized in the recent 655
Gigabyte attack against Brian Krebs’s website, we could soon see
new records broken in the DDoS attack landscape, with potential to
reach tens of Terabits per second in size in the not too distant
future. The DDoS landscape has been extremely volatile in recent
weeks, particularly with the release of the Mirai code and
subsequent Mirai infected Internet of Things (IoT) devices, and we
expect this trend to continue for the foreseeable future.
Dave Larson, CTO/COO at Corero Network Security, explains: “This
new vector may represent a substantial escalation in the already
dangerous DDoS landscape, with potential for events that will make
recent attacks that have been making headlines seem small by
comparison. When combined with other methods, particularly IoT
botnets, we could soon see attacks reaching previously unimaginable
scale, with far-reaching impact. Terabit scale attacks could soon
become a common reality and could significantly impact the
availability of the Internet– at least degrading it in certain
regions.”
Reflection and amplification attacks
In this case, the attacker sends a simple query to a vulnerable
reflector supporting the Connectionless LDAP service (CLDAP) and
using address spoofing makes it appear to originate from the
intended victim. The CLDAP service responds to the spoofed address,
sending unwanted network traffic to the attacker’s intended
target.
Amplification techniques allow bad actors to intensify the size
of their attacks, because the responses generated by the LDAP
servers are much larger than the attacker’s queries. In this case,
the LDAP service responses are capable of reaching very high
bandwidth and we have seen an average amplification factor of 46x
and a peak of 55x.
Dave Larson explains: “LDAP is not the first, and will not be
the last, protocol or service to be exploited in this fashion.
Novel amplification attacks like this occur because there are so
many open services on the Internet that will respond to spoofed
record queries. However, a lot of these attacks could be eased by
proper service provider hygiene, by correctly identifying spoofed
IP addresses before these requests are admitted to the network.
Specifically, following the best common practice, BCP 38, described
in the Internet Engineering Task Force (IETF) RFC 2827, which
describes router configurations that are designed to eliminate
spoofed IP address usage by employing meaningful ingress filtering
techniques, would reduce the overall problem of reflected DDoS by
at least an order of magnitude.
“Today’s DDoS attacks are increasingly automated, meaning that
attackers can switch vectors faster than any human can respond. The
only effective defense against this type of DDoS attack vector
requires automated mitigation techniques. Relying on out-of-band
scrubbing DDoS protection to stop these attacks will cause
significant collateral damage. Given the short duration and high
volume attacks, legacy solutions simply cannot identify and
properly mitigate in time to protect network availability.”
The CLDAP zero-day attacks targeted at Corero
customers were automatically mitigated by the Corero
SmartWall® Threat Defense System with patented Smart Rule
functionality. No human intervention was necessary in mitigating
this previously unknown DDoS attack vector and no outages were
caused as a result of these attacks in the Corero customer
base.
About Corero Network Security
Corero Network Security is the leader in real-time,
high-performance DDoS defense solutions. Service providers, hosting
providers and online enterprises rely on Corero’s award winning
technology to eliminate the DDoS threat to their environment
through automatic attack detection and mitigation, coupled with
complete network visibility, analytics and reporting. This
next-generation technology provides a First Line of Defense®
against DDoS attacks in the most complex environments while
enabling a more cost effective economic model than previously
available. For more information, visit www.corero.com.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20161025005921/en/
Elevate CommunicationsJohn Gates,o-617-861-3651;
m-617-548-8972corero@elevatecom.com
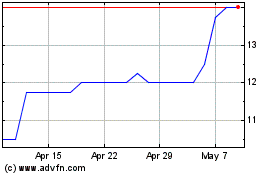
Corero Network Security (LSE:CNS)
Historical Stock Chart
From Apr 2024 to May 2024
Corero Network Security (LSE:CNS)
Historical Stock Chart
From May 2023 to May 2024
