Ransomware Doubled in Second Half of 2016, says Check Point
February 21 2017 - 8:00AM

Check Point® Software Technologies Ltd. (Nasdaq:CHKP), today
released its H2 2016 Global Threat Intelligence Trends,
revealing that ransomware attacks doubled during the period.
Out of all recognized malware incidents globally, the percentage of
ransomware attacks increased from 5.5% to 10.5% between July and
December 2016.
The H2 2016 Global Threat Intelligence Trends Report highlights
the key tactics cyber-criminals are using to attack businesses, and
gives a detailed overview of the cyber-threat landscape in the top
malware categories – ransomware, banking and mobile. It is based on
threat intelligence data drawn from Check Point’s ThreatCloud World
Cyber Threat Map between July and December 2016.
Key trendsCheck Point researchers detected a
number of key trends during the period:
- The Monopoly in the Ransomware Market –
thousands of new ransomware variants were observed in 2016, and in
recent months we witnessed a change in the ransomware landscape as
it became more and more centralized, with a few significant malware
families dominating the market and hitting organizations of all
sizes.
- DDoS Attacks via IoT Devices – in August 2016,
the infamous Mirai Botnet was discovered – a first of its kind the
Internet-of-Things (IoT) Botnet, which attacks vulnerable
Internet-enabled digital such as video recorders (DVR) and
surveillance cameras (CCTV). It turns them into bots, using the
compromised devices to launch multiple high-volume Distributed
Denial of Service (DDoS) attacks. It is now clear that vulnerable
IoT devices are in use in almost every home, and massive DDoS
attacks that are based on such will persist.
- New File Extensions Used in Spam Campaigns –
the most prevalent infection vector used in malicious spam
campaigns throughout the second half 2016 was downloaders based on
Windows Script engine (WScript). Downloaders written in Javascript
(JS) and VBScript (VBS) dominated the mal-spam distribution field,
together with similar yet less familiar formats such as JSE, WSF,
and VBE.
Top malware during H2 2016:
- Conficker (14.5%) - Worm that allows remote
operations and malware download. The infected machine is controlled
by a botnet, which contacts its Command & Control server to
receive instructions.
- Sality (6.1%) - Virus that allows remote
operations and downloads of additional malware to infected systems
by its operator. Its main goal is to persist in a system and
provide means for remote control and installing further
malware.
- Cutwail (4.6%) - Botnet mostly involved in
sending spam e-mails, as well as some DDOS attacks. Once
installed, the bots connect directly to the command and control
server, and receive instructions about the emails they should send.
After they are done with their task, the bots report back to the
spammer exact statistics regarding their operation.
- JBossjmx (4.5%) - Worm that targets systems
having a vulnerable version of JBoss Application Server installed.
The malware creates a malicious JSP page on vulnerable systems that
executes arbitrary commands. Moreover, another Backdoor is created
that accepts commands from a remote IRC server.
- Locky (4.3%) - Ransomware, which started its
distribution in February 2016, and spreads mainly via spam emails
containing a downloader disguised as a Word or Zip file attachment,
which then downloads and installs the malware that encrypts the
user files.
Top ransomware during H2 2016:The percentage of
ransomware attacks out of all recognized attacks globally almost
doubled in the second half of 2016, from 5.5% to 10.5%. The most
common variants detected were:
- Locky 41% - The third most common ransomware
in H1, which increased dramatically in the second half of the
year.
- Cryptowall 27% - Ransomware that started as a
Cryptolocker doppelgänger, but eventually surpassed it. After the
takedown of Cryptolocker, Cryptowall became one of the most
prominent ransomwares to date. Cryptowall is known for its use of
AES encryption and for conducting its C&C communications over
the Tor anonymous network. It is widely distributed via exploit
kits, malvertising and phishing campaigns.
- Cerber 23% - the world’s biggest
ransomware-as-a-service scheme. Cerber is a franchise scheme,
with its developer recruiting affiliates who spread the malware for
a cut of the profits.
Top Mobile Malware during H2 2016:
- Hummingbad 60% - Android malware first
revealed by Check Point research team that establishes a persistent
rootkit on the device, installs fraudulent applications and with
slight modifications could enable additional malicious activity
such as installing a key-logger, stealing credentials and bypassing
encrypted email containers used by enterprises.
- Triada 9% - Modular Backdoor for Android which
grants superuser privileges to downloaded malware, and helps it to
get embedded into system processes. Triada has also been seen
spoofing URLs loaded in the browser.
- Ztorg 7% – Trojan that uses root privileges to
download and install applications on the mobile phone without the
user’s knowledge.
Top banking malware:
- Zeus 33% - Trojan that targets Windows
platforms and is often used to steal banking information by
man-in-the-browser keystroke logging and form grabbing.
- Tinba 21% - Banking Trojan that steals the
victim’s credentials using web-injects, activated as the users try
to login to their bank website.
- Ramnit 16% – Banking Trojan that steals
banking credentials, FTP passwords, session cookies and personal
data.
Maya Horowitz, Threat Intelligence Group
Manager at Check Point commented: “The report demonstrates the
nature of today’s cyber environment, with ransomware attacks
growing rapidly. This is simply because they work, and generate
significant revenues for attackers. Organizations are struggling to
effectively counteract the threat: many don't have the right
defenses in place, and may not have educated their staff on how to
recognize the signs of a potential ransomware attack in incoming
emails.”
“Additionally our data demonstrates that a small number of
families are responsible for the majority of attacks, while
thousands of other malware families are rarely seen,” continued
Horowitz. “Most cyber threats are global and cross-regional, yet
the APAC region, stands out as its Top Malware Families chart
includes 5 families which do not appear in the other regional
charts.”
The statistics in this report are based on data drawn from the
ThreatCloud World Cyber Threat Map. Check Point’s ThreatCloud is
the largest collaborative network to fight cybercrime, delivering
the most up-to-date threat data and cyberattack trends from a
global network of threat sensors. The ThreatCloud database
identifies millions of malware types daily, and contains more than
250 million addresses analyzed for bot discovery, as well as over
11 million malware signatures and 5.5 million infected
websites.
A full copy of the report can be found here.
Follow Check Point via:Check Point Blog:
http://blog.checkpoint.com/ Twitter:
http://www.twitter.com/checkpointsw Facebook:
http://www.facebook.com/checkpointsoftware YouTube:
http://www.youtube.com/user/CPGlobal LinkedIn:
https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest network cyber security vendor
globally, providing industry-leading solutions and protecting
customers from cyberattacks with an unmatched catch rate of malware
and other types of threats. Check Point offers a complete security
architecture defending enterprises – from networks to mobile
devices – in addition to the most comprehensive and intuitive
security management. Check Point protects over 100,000
organizations of all sizes.
INVESTOR CONTACT:
Kip E. Meintzer
Check Point Software Technologies
+1.650.628.2040
ir@checkpoint.com
MEDIA CONTACT:
Emilie Beneitez Lefebvre
Check Point Software Technologies
Tel: +44 (0) 7785 381 302
press@checkpoint.com
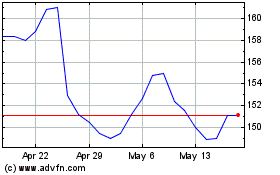
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2024 to May 2024
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2023 to May 2024
