Survey: Only Half of Organizations Believe They Can Stop Cyber Attacks
July 23 2019 - 7:30AM
Business Wire
CyberArk Report Also Finds Agility and
Automation Initiatives May Lead to ‘Credential Creep’ and Increased
Privilege-Related Risk
According to a new global survey from CyberArk (NASDAQ: CYBR),
50 percent of organizations believe attackers can infiltrate their
networks each time they try. As organizations increase investments
in automation and agility, a general lack of awareness about the
existence of privileged credentials – across DevOps, robotic
process automation (RPA) and in the cloud – is compounding
risk.
This press release features multimedia. View
the full release here:
https://www.businesswire.com/news/home/20190723005131/en/
(Graphic: Business Wire)
According to the CyberArk Global Advanced Threat Landscape 2019
Report, less than half of organizations have a privileged access
security strategy in place for DevOps, IoT, RPA and other
technologies that are foundational to digital initiatives. This
creates a perfect opportunity for attackers to exploit legitimate
privileged access to move laterally across a network to conduct
reconnaissance and progress their mission.
Preventing this lateral movement is a key reason why
organizations are mapping security investments against key
mitigation points along the cyber kill chain, with 28 percent of
total planned security spend in the next two years focused on
stopping privilege escalation and lateral movement.
Proactive investments to reduce risk are critical given what
this year’s survey respondents cite as their top threats:
- 78 percent identified hackers in their top three greatest
threats to critical assets, followed by organized crime (46
percent), hacktivists (46 percent) and privileged insiders (41
percent).
- 60 percent of respondents cited external attacks, such as
phishing, as one of the greatest security risks currently facing
their organization, followed by ransomware (59 percent) and Shadow
IT (45 percent).
Security Barriers to Digital Transformation and the Privilege
Priority The survey found that while organizations view
privileged access security as a core component of an effective
cybersecurity program, this understanding has not yet translated to
action for protecting foundational digital transformation
technologies.
- 84 percent state that IT infrastructure and critical data are
not fully protected unless privileged accounts, credentials and
secrets are secured.
- Despite this, only 49 percent have a privileged access security
strategy in place for protecting business critical applications and
cloud infrastructure respectively, with even fewer having a
strategy for DevOps (35 percent) or IoT (32 percent).
- Further, only 21 percent understood that privileged accounts,
credentials and secrets exist in containers, 24 percent understood
that they exist in source code repositories and 30 percent
understood that they are present in privileged applications and
processes such as RPA.
“Organizations are showing increasing understanding of the
importance of mitigation along the cyber kill chain and why
preventing credential creep and lateral movement is critical to
security,” said Adam Bosnian, executive vice president, global
business development, CyberArk. “But this awareness must extend to
consistently implementing proactive cybersecurity strategies across
all modern infrastructure and applications, specifically reducing
privilege-related risk in order to recognize tangible business
value from digital transformation initiatives.”
Global Compliance Readiness According to the survey, a
surprising 41 percent of organizations would be willing to pay
fines for non-compliance with major regulations, but would not
change security policies even after experiencing a successful cyber
attack. On the heels of more than $300M in General Data Protection
Regulation (GDPR) fines being levied on global organizations for
data breaches, this mindset is not sustainable.
The survey also examined the impact of major regulations around
the world:
- GDPR: Less than half (46 percent) are completely
prepared for breach notification and investigation within the
mandated 72 hour period.
- Australia’s Data Breach Notification Law: 62 percent of
Australian respondents reported that they were completely prepared
to comply with the entirety of the statute, which came into force
in February 2019.
- California Consumer Privacy Act (CCPA): Only 37 percent
are ready for this legislation to go into effect in 2020; 39
percent are actively working to meet deadline requirements.
About the CyberArk Advanced Threat Landscape 2019 Report
The CyberArk Global Advanced Threat Landscape 2019 annual report is
the 12th in the series. The survey was conducted by Vanson Bourne
among 1,000 IT security decision makers and C-level executives
across seven countries worldwide: the US, UK, France, Germany,
Israel, Singapore and Australia. To download a copy of the report,
please visit: http://www.cyberark.com/TL19
Additional Resources
- Infographic: Attackers Seek To Shortcut The Path To
Privileged Credentials Compromise
- Report: CyberArk Global Advanced Threat Landscape Report
2019: Focus on Cloud
About CyberArk CyberArk (NASDAQ: CYBR) is the global
leader in privileged access security, a critical layer of IT
security to protect data, infrastructure and assets across the
enterprise, in the cloud and throughout the DevOps pipeline.
CyberArk delivers the industry’s most complete solution to reduce
risk created by privileged credentials and secrets. The company is
trusted by the world’s leading organizations, including more than
50 percent of the Fortune 500, to protect against external
attackers and malicious insiders. A global company, CyberArk is
headquartered in Petach Tikva, Israel, with U.S. headquarters
located in Newton, Mass. The company also has offices throughout
the Americas, EMEA, Asia Pacific and Japan. To learn more about
CyberArk, visit www.cyberark.com, read the CyberArk blogs or follow
on Twitter via @CyberArk, LinkedIn or Facebook.
Copyright © 2019 CyberArk Software. All Rights Reserved. All
other brand names, product names, or trademarks belong to their
respective holders.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20190723005131/en/
Media Relations Contacts: Brian Merrill, fama PR Phone:
+1-617-986-5005 Email: cyberark@famapr.com Liz Campbell, CyberArk Phone:
+1-617-558-2191 Email: press@cyberark.com Investor Relations
Contact: Erica Smith, CyberArk Phone: +1 617-630-6426 Email:
ir@cyberark.com
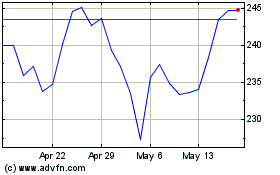
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From Apr 2024 to May 2024
CyberArk Software (NASDAQ:CYBR)
Historical Stock Chart
From May 2023 to May 2024
