Show Me The Money: Cybercriminals Deploying Diverse Range of Banking Trojans and Ransomware, says Check Point
September 18 2017 - 8:00AM

Check Point® Software Technologies Ltd. (NASDAQ:CHKP) revealed that
banking trojans were extensively used by cyber-criminals during
August, with three variants appearing in the company’s latest
Global Threat Impact Index.
The Zeus, Ramnit and Trickbot banking trojans all appeared in
the top ten. These Trojans work by identifying when the
victim is visiting a banking website, and then use keylogging or
webinjects to harvest basic login credentials or more sensitive
information such as PIN numbers. Alternatively, Trojans may also
direct victims to fake banking websites designed to mimic the
legitimate ones and steal credentials that way.
The August Global Threat Impact Index also revealed that
Globeimposter, a ransomware disguised as a variant of the Globe
ransomware, was the world’s second most prevalent malware
throughout the month. Although it was discovered in May 2017, the
malware did not begin to rapidly proliferate until August,
distributed by spam campaigns, malvertising and exploit kits. Upon
encryption, Globeimposter appends the .crypt extension to each
encrypted file, and a payment is demanded from victims in return
for decrypting their valuable data.
“Financial gain is the major motive for the vast majority of
cybercrime, and unfortunately criminals have a wide range of tools
at their disposal to achieve this,” said Maya Horowitz, Threat
Intelligence, Group Manager at Check Point. “To see both a
highly effective ransomware variant and a range of banking Trojans
in the top ten most prevalent malware families really underlines
how tenacious and sophisticated malicious hackers can be in their
attempts to extort money. Organizations need to be both vigilant
and proactive in order to protect their networks.”
August 2017’s Top 3 ‘Most Wanted’ Malware:*The
arrows relate to the change in rank compared to the previous
month.Roughted remained the top malware in August, although its
global impact decreased from 18% to under 12% of organizations
worldwide. Globalimposter in second place had a global impact of 6%
and HackerDefender in third place with 4% global impact.
- ↔ Roughted - Large scale Malvertising used to
deliver various malicious websites and payloads such as scams,
adware, exploit kits and ransomware. It can be used to attack any
type of platform and operating system, and utilizes ad-blocker,
bypassing and fingerprinting in order to make sure it delivers the
most relevant attack.
- ↑ Globeimposter - Ransomware disguised as a
variant of the Globe ransomware. It was discovered in May 2017, and
is distributed by spam campaigns, malvertising and exploit kits.
Upon encryption, the ransomware appends the .crypt extension to
each encrypted file.
- ↓ HackerDefender - User-mode Rootkit for
Windows. Can be used to hide files, processes and registry
keys, and also implements a backdoor and port redirector that
operates through TCP ports opened by existing services. This means
it is not possible to find the hidden backdoor through traditional
means.
Hummingbad, which appeared in the top ten every month in the
first half of 2017, did not make a re-appearance. The most popular
malware used to attack organizations’ mobile assets changed in
August, with Triada moving up from third place, followed by Hiddad
and Gooligan:
Top 3 ‘Most Wanted’ mobile malware:
- Triada - Modular Backdoor for Android which
grants super-user privileges to downloaded malware, which helps the
malware become embedded into system processes. Triada has also been
seen spoofing URLs loaded in the browser.
- Hiddad - Android malware which repackages
legitimate apps and then releases them to a third-party store. Its
main function is displaying ads, however it is also able to gain
access to key security details built into the OS, allowing an
attacker to obtain sensitive user data.
- Gooligan - Android malware capable of
rooting devices and stealing email addresses and authentication
tokens stored on the device.
The August Threat Index shows just how diverse and dynamic the
cyber threat landscape is. Just a few months ago, Hummingbad was
incredibly dominant; however in August it did not even make it into
the top ten. Similarly, ransomware has been grabbing most of the
cybersecurity headlines, yet well-established banking Trojans are
on the rise again.
“It’s vital for organizations to be alert to these
shifting threats, to simultaneously keep their defenses up against
well-known malware families, new variants and new zero-day
threats,” added Horowitz. “This requires a multi-layered
cybersecurity strategy, which can respond to a broad range of
continually evolving attack types.”
Check Point’s Global Threat Impact Index and its ThreatCloud Map
is powered by Check Point’s ThreatCloud intelligence, a
collaborative network to fight cybercrime which delivers threat
data and attack trends from a global network of threat sensors. The
ThreatCloud database holds over 250 million addresses analyzed for
bot discovery, more than 11 million malware signatures and over 5.5
million infected websites, and identifies millions of malware types
daily.
* The complete list of the top 10 malware families in August can
be found on the Check Point Blog:
//dm-research.us.checkpoint.com/augusts-most-wanted-malware-banking-trojans-and-ransomware-that-want-your-money/
Check Point’s Threat Prevention Resources are available
at:
http://www.checkpoint.com/threat-prevention-resources/index.html
Follow Check Point
via:Twitter: http://www.twitter.com/checkpointswFacebook: https://www.facebook.com/checkpointsoftwareBlog:
http://blog.checkpoint.com
YouTube: http://www.youtube.com/user/CPGlobalLinkedIn: https://www.linkedin.com/company/check-point-software-technologies
About Check Point Software Technologies
Ltd.Check Point Software Technologies Ltd.
(www.checkpoint.com) is the largest pure-play security vendor
globally, provides industry-leading solutions, and protects
customers from cyberattacks with an unmatched catch rate of malware
and other types of attacks. Check Point offers a complete security
architecture defending enterprises’ networks to mobile devices, in
addition to the most comprehensive and intuitive security
management. Check Point protects over 100,000 organizations of all
sizes.
INVESTOR CONTACT:Kip E. MeintzerCheck Point
Software Technologies+1.650.628.2040ir@checkpoint.com
MEDIA CONTACT:Emilie Beneitez LefebvreCheck
Point Software TechnologiesTel: +44 (0) 7785 381
302press@checkpoint.com
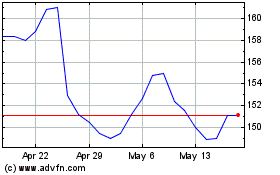
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From Apr 2024 to May 2024
Check Point Software Tec... (NASDAQ:CHKP)
Historical Stock Chart
From May 2023 to May 2024
